
your software,
tended.
Maxx keeps every app on your Mac current, verified, and auditable.
Where competitors stop at detection, Maxx acts.

Maxx keeps every app on your Mac current, verified, and auditable.
Where competitors stop at detection, Maxx acts.
MacUpdater's backend went dark. 238 apps lost their update path overnight. Homebrew covers some. The App Store covers others. The rest drift — quietly accumulating security debt — until a CVE shows up and you realise you've been running a vulnerable version for four months.
Apps outside Homebrew or the MAS have no automatic update path. They fall behind silently.
You can't tell if a "Chrome update" is actually Chrome. TeamID verification closes that gap.
When did that app update? From where? What changed? Without provenance, you're guessing.
Every update Maxx installs passes through the same four-step protocol. No shortcuts. No blind trust. The protocol is open source — you can read every line.

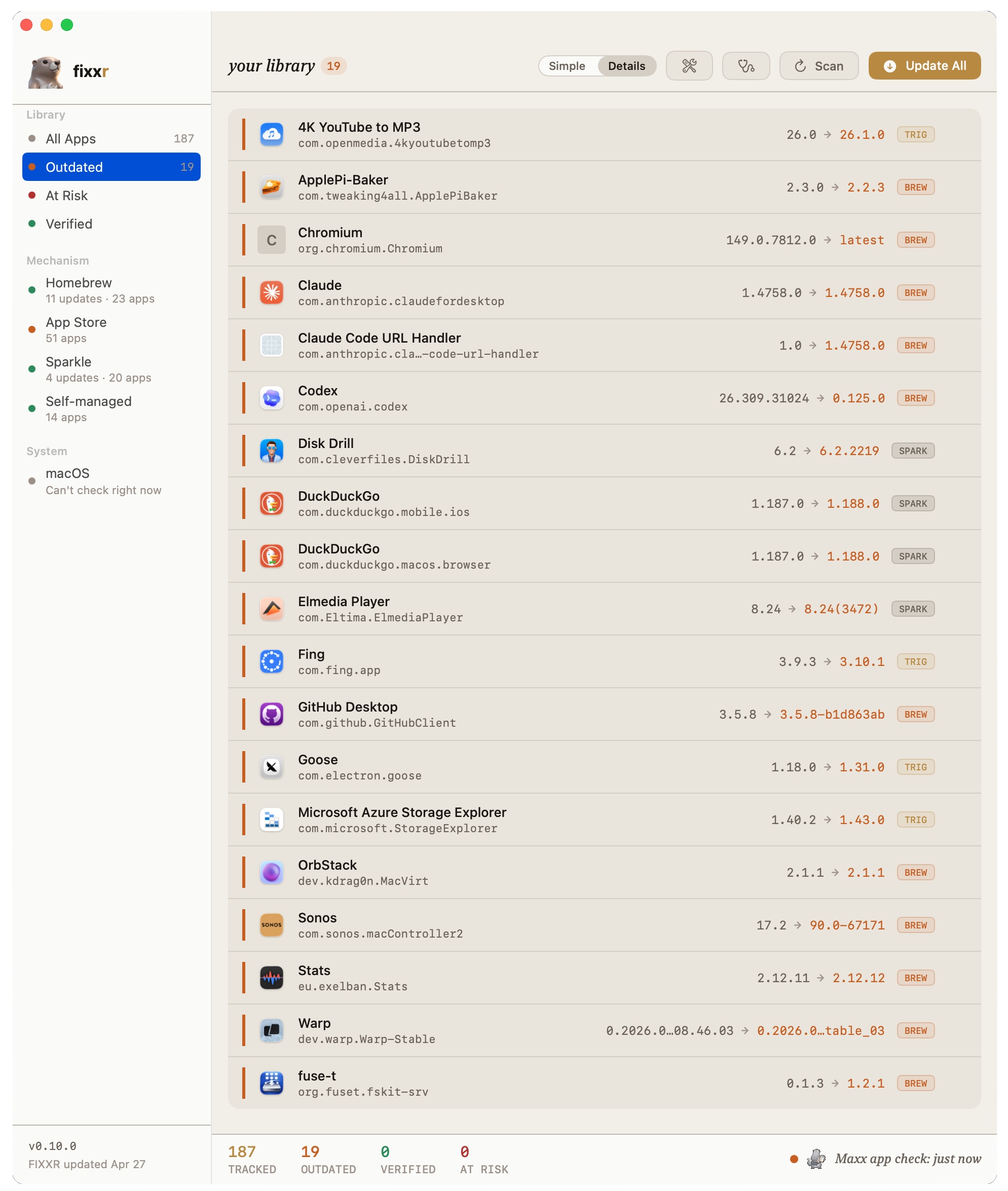
Maxx queries Sparkle feeds, Homebrew Cask, the Mac App Store, and 25+ vendor self-updaters (Google Software Update, Microsoft AutoUpdate, Squirrel apps). He finds what's new across all five update mechanisms so nothing slips through.
SUFeedURL parsed from app plists via scan_feeds.py. Homebrew Cask JSON via cask_agent.py. App Store apps via mdfind kMDItemAppStoreHasReceipt. Vendor self-updaters detected by self_updater_probe.py against a 25-fingerprint library.

TeamID from codesign -dvv is compared against the installed app. New TeamID = blocked. The community catalog adds consensus SHA256 verification across endpoints that have already trusted the same binary.
TeamID extracted via codesign -dvv. SHA256 computed via shasum -a 256. Consensus pulled from the community catalog and compared against local hash.
Before any rights elevation: CDN origin, URL patterns, the Internet Access Policy manifest, and an optional Claude Opus 4.7 second opinion. High confidence installs automatically. Low confidence queues for your review.
Install gatekeeper at install_safety.py. IAP read from the bundle via iap_reader.py. AI second opinion gated by FIXXR_OPUS_KEY env.
Every update — success or failure — is recorded in a local SQLite ledger. Who, what, from where, when. You own the full provenance trail. The Green Seal stamps a row only when TeamID, SHA256, and CDN domain all line up.
Storage: WAL-mode SQLite at ~/.fixxr/fixxr.db. Every mutation written to changelog with a timestamp. Privacy-filtered push to the community catalog via the PUBLISH_FIELDS allowlist — never the whole row.
Maxx routes each app to the best mechanism automatically — Homebrew Cask, the App Store, Sparkle, native triggers, vendor self-updaters. Five mechanisms, one protocol, one CLI surface.
Maxx queries every source in parallel. No manual configuration — he reads your installed apps and figures out where they update from.
fixxr scanDays outdated × security tier. A browser 47 days behind ranks above a utility that just hit a minor version.
fixxr list --riskAI assessment runs before every rights elevation. Suspicious installs queue for your review. Everything else completes automatically.
fixxr updateWhere did this binary come from? What CDN? Was the TeamID consistent? SHA256 consensus from the community catalog?
fixxr provenanceTotal apps tracked, outdated count, CVE exposure, mean days outdated, pending safety reviews — in a single report.
fixxr reportNot a checkmark. An actual stamp — the visual payoff for the whole provenance system. When Maxx earns it, he puts his mark on the work.
TeamID chain unbroken. The new binary's signing identity matches the installed app. Same developer, verifiably.
SHA256 matches community consensus. Other FIXXR users saw the same binary. Or self-verified on first download and cached locally.
CDN domain consistent. Mozilla doesn't suddenly update from a domain in Russia. Google doesn't deliver Chrome from a sketchy CDN. Drift is caught.
The library is in order. Every tool verified and in its place.
Depth is unlocked, not forced. Each tier maps to one of Maxx's three hats — Sentry watches, Craftsman works, Curator keeps the ledger. A personal Mac user gets the first two. A security engineer gets the deeper two. Same Maxx, same protocol.
Know what's installed, what's outdated, and how far behind. Across all five mechanisms — Homebrew, App Store, Sparkle, vendor self-updaters, native triggers. The baseline every Mac user should have.
Actually install the updates. Maxx routes to the right mechanism — and steps back when an app self-updates (Self-managed bucket). One command, five mechanisms, no double-installs.
Know where every binary came from. TeamID verification, SHA256, CDN tracking, the Green Seal. Every install written to a local SQLite ledger you can query.
CVE correlation against OSV.dev. Risk-ranked updates. AI safety gatekeeper (Claude Opus 4.7). Community checksum consensus. The full platform — Sentry, Craftsman, and Curator in concert.
The FIXXR community catalog is an open dataset of verified app provenance. Every participant makes the catalog smarter for everyone who follows.
An open database of macOS app provenance: download URLs, TeamIDs, SHA256 checksums, update mechanisms. Opt-in push contributes your verified data. Privacy filter enforced in code — only whitelisted fields ever leave your machine.
Sync via HTTP POST to Cloudflare D1. Only PUBLISH_FIELDS leave your machine: bundle_id, app_name, latest_version, download_url, sha256, feed_url, homepage_url, update_mechanism. Enforced at the adapter layer in db.py.
For the ~53 third-party apps with no automation record, you can help Maxx learn.
Run fixxr watch "App Name" while manually updating an app — Maxx monitors network connections, detects the CDN and download pattern, and records the mechanism.
Opt-in with fixxr community enable --help-maxx to share what you discover.
Your observation becomes the next person's automation.
When multiple FIXXR users download the same version of the same app, their SHA256 hashes should match. A mismatch is a supply chain incident. The catalog tracks consensus — if your hash diverges from 47 other endpoints, you'll know. Architecture differences (arm64 vs universal) are annotated to avoid false alerts.
Maxx queries OSV.dev for known vulnerabilities in every installed app version, cached locally to avoid repeated API calls.
Run fixxr cve to scan your full inventory. Results surface in fixxr report and fixxr list --risk — CVE exposure moves an app up the priority queue automatically.
A Verein is a Swiss non-profit association — the governance structure for projects that belong to a community, not a company. The FIXXR Verein is the entity being formed to steward the protocol, the catalog, and the open-source codebase over the long term.
Any individual or organisation can become a member. Governance is democratic. No single entity controls the protocol.
The Verein's accounts, decisions, and membership are public. Inspired by Objective Development's IAP model — declare what you do and be held to it.
The Verein maintains the FIXXR Protocol specification, the community catalog, and the domain fixxr.org.
Membership dues fund infrastructure (hosting, CI, and the public catalog). The software stays MIT-licensed, free to use, fork, and self-host.

The library belongs to everyone who tends it.
Inspired by Objective Development's Internet Access Policy model.
Maxx-as-Curator declares exactly what data exists locally, what you can share, and what never leaves your machine.
Run fixxr privacy --audit to see the actual stored data alongside the policy.
fixxr watch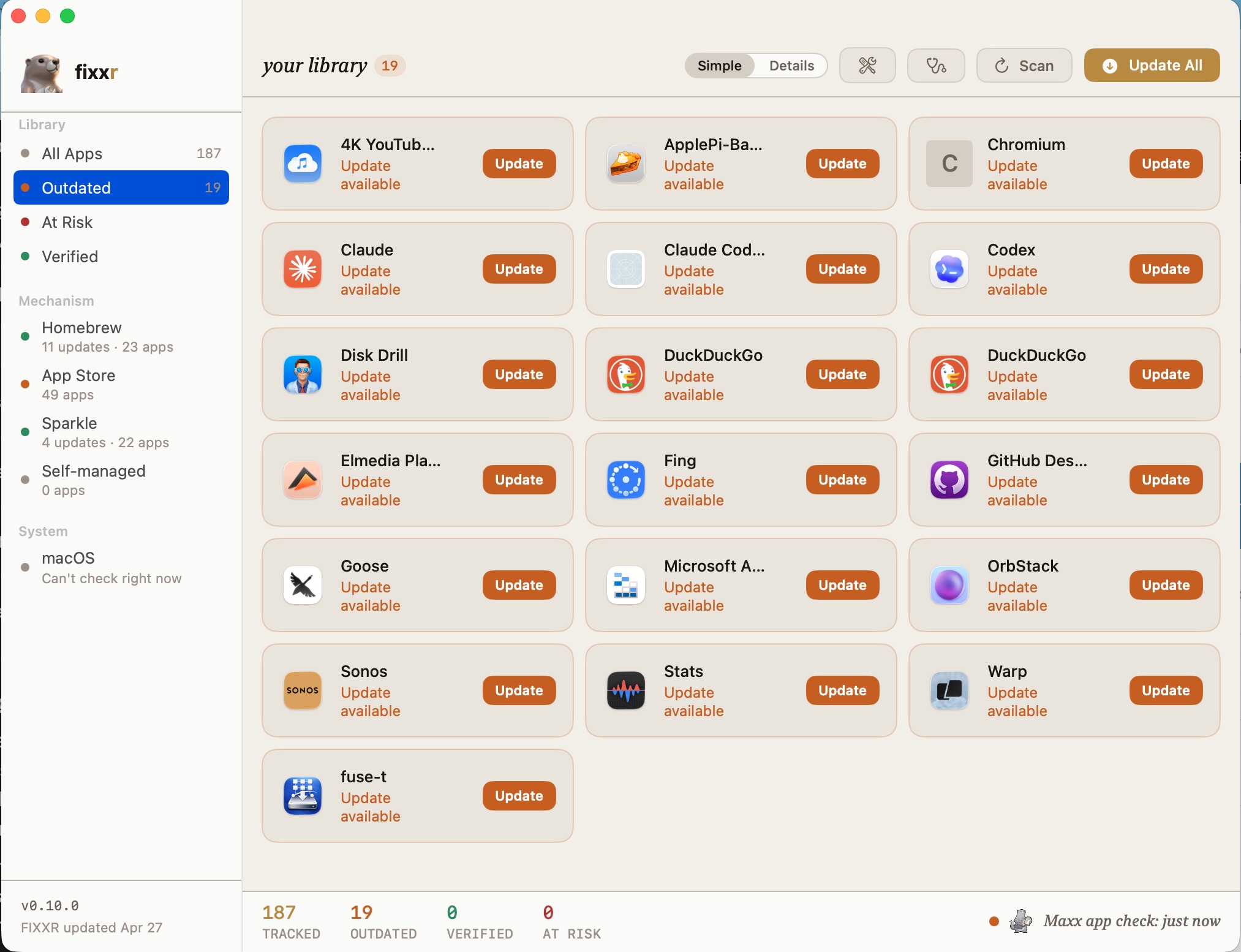
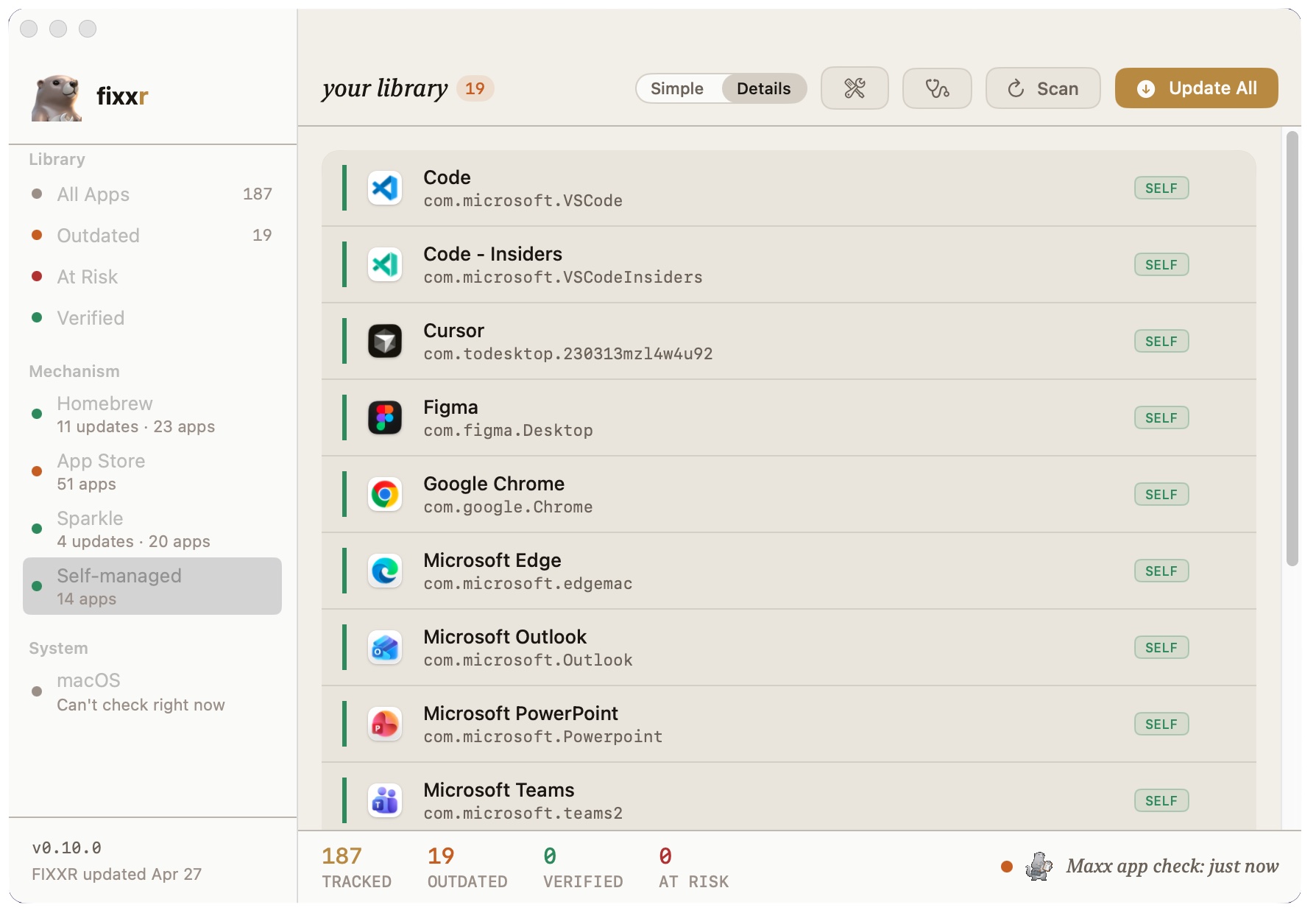
SELF, and observes. Honest about who's holding the wrench.
Menu bar app + CLI in one package.
Drag to Applications. No terminal required.
Maxx starts scanning immediately.
Signed and notarized. macOS 13+. No dependencies.
shasum -a 256 FIXXR-*.dmg
For developers and IT teams.
CLI-only setup with optional Homebrew integration.
curl -sSL https://fixxr.org/install.sh | bash
copy
macOS 13 Ventura or later · Apple Silicon and Intel supported · No dependencies required for the app
Homebrew integration available as an optional enhancement after install
Read the about page first if you prefer to review before running install scripts.
The installer source is at fixxr.org/install.sh and in the GitHub repo.